Traffic Server provides a number of security features.
This chapter discusses the following topics:
You can configure Traffic Server to allow only certain clients to use the proxy cache by editing a configuration file.
ip_allow.config file located in the Traffic Server config directory. ip_allow.config file. bin directory.traffic_line -x to apply the configuration changes.By restricting access to Traffic Server, you ensure that only authenticated users can change configuration options and view network traffic statistics.
Traffic Server supports the Secure Sockets Layer (SSL) protocol to provide protection for remote administrative monitoring and configuration. SSL security provides authentication for both ends of a network connection via certificates and provides privacy via encryption.
To use SSL, you must do the following:
The SSL certificate is a text file you must install in the Traffic Server config directory. Either rename the certificate to the default filename private_key.pem, or specify the name of the certificate in the configuration file (follow the procedure in Enabling SSL).
After you've obtained an SSL certificate, enable SSL by manually editing a configuration file. Follow the steps below:
records.config file located in the Traffic Server config directory. | Variable | Description |
|---|---|
proxy.config.admin.use_ssl |
Set this variable to 1 to enable SSL. |
proxy.config.admin.ssl_cert_file |
Set this variable to specify the filename of the SSL certificate. You have to change the filename only if the certificate file does not use the default name private_key.pem. |
records.config file. bin directory.traffic_line -x to apply the configuration changes.The Split DNS option enables you to configure Traffic Server to use multiple DNS servers, as dictated by your security requirements. For example, you might configure Traffic Server to use one set of DNS servers to resolve hostnames on your internal network, while allowing DNS servers outside the firewall to resolve hosts on the Internet. This maintains the security of your intranet, while continuing to provide direct access to sites outside your organization.
To configure Split DNS, you must do the following:
splitdns.config file located in the Traffic Server config directory. splitdns.config file. For information about the format of the splitdns.config file, click here. splitdns.config file.records.config file located in the Traffic Server config directory. | Variable | Description |
|---|---|
proxy.process.dns.splitDNS.enabled |
Set this variable to 1 to enable split DNS. |
proxy.config.dns.splitdns.def_domain |
Set this variable to specify the default domain for split DNS requests. Traffic Server appends this value automatically to a hostname that does not include a domain before determining which DNS server to use. |
records.config file. bin directory. traffic_line -x to apply the configuration changes. The Traffic Server SSL termination option enables you to secure connections in reverse proxy mode between a client and a Traffic Server and/or Traffic Server and an origin server.
The following sections describe how to enable and configure the SSL termination option.
If you install an SSL accelerator card on your Traffic Server system, then you must perform additional configuration steps - refer to Configuring Traffic Server to Use an SSL Accelerator Card.
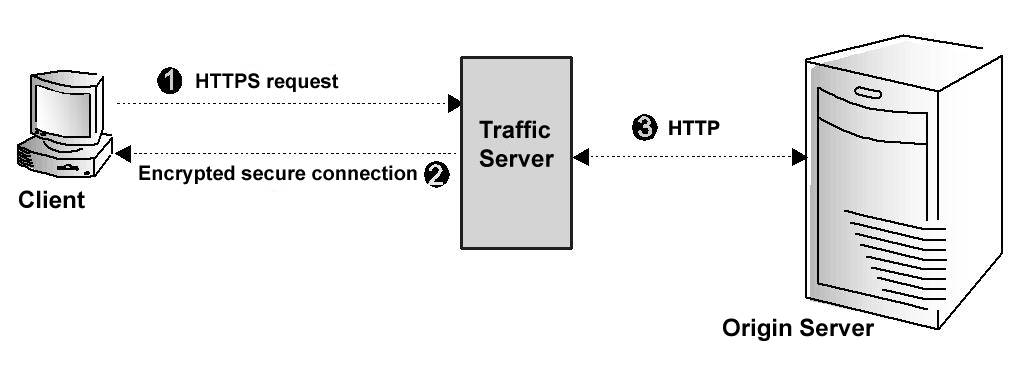
The figure below illustrates communication between a client and Traffic Server (and between Traffic Server and an origin server) when the SSL termination option is enabled & configured for client/Traffic Server connections only.
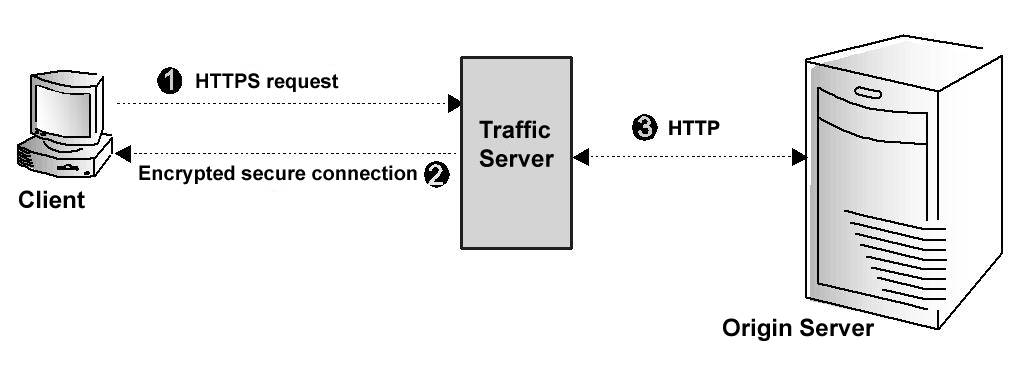
Client and Traffic Server communication using SSL termination
The figure above depicts the following:
Step 1: The client sends an HTTPS request for content. Traffic Server receives the request and performs the SSL 'handshake' to authenticate the client (depending on the authentication options configured) and determine the encryption method that will be used. If the client is allowed access, then Traffic Server checks its cache for the requested content.
Step 2: If the request is a cache hit and the content is fresh, thenTraffic Server encrypts the content and sends it to the client. The client decrypts the content (using the method determined during the handshake) and displays it.
Step 3: If the request is a cache miss or cached content is stale, then Traffic Server communicates with the origin server via HTTP and obtains a plain text version of the content. Traffic Server saves the plain text version of the content in its cache, encrypts the content, and sends it to the client. The client decrypts and displays the content.
To configure Traffic Server to use the SSL termination option for client/Traffic Server connections, you must do the following:
ip_allow.config file). records.config file located in the Traffic Server config directory. SSL Termination section of the file: | Variable | Description |
|---|---|
proxy.config.ssl.enabled |
Set this variable to 1 to enable the SSL termination option. |
proxy.config.ssl.server_port |
Set this variable to specify the port used for SSL communication. The default port is 443. |
proxy.config.ssl.client.certification_level |
Set this variable to one of the following values:0 - no client certificates are required. Traffic Server does not verify client certificates during the SSL handshake. Access to Traffic Server depends on Traffic Server configuration options (such as access control lists).1 - client certificates are optional. If a client has a certificate, then the certificate is validated. If the client does not have a certificate, then the client is still allowed access to Traffic Server unless access is denied through other Traffic Server configuration options.2 - client certificates are required. The client must be authenticated during the SSL handshake; Clients without a certificate are not allowed to access Traffic Server. |
proxy.config.ssl.server.cert.filename |
Set this variable to specify the filename of the Traffic Server SSL server certificate. Traffic Server provides a demo server certificate called server.pem - use this certificate to verify that the SSL feature is working.If you are using multiple server certificates, then set this variable to specify the default filename. |
proxy.config.ssl.server.cert.path |
Set this variable to specify the location of the Traffic Server SSL server certificate. The default directory is the Traffic Server config directory. |
proxy.config.ssl.server.private_key.filename |
Set this variable to specify the filename of the Traffic Server private key. Change this variable only if the private key is not located in the Traffic Server SSL server certificate file. |
proxy.config.ssl.server.private_key.path |
Set this variable to specify the location of the Traffic Server private key. Change this variable only if the private key is not located in the Traffic Server SSL server certificate file. |
proxy.config.ssl.CA.cert.filename |
Specify the filename of the certificate authority that client certificates will be verified against. The default value is NULL. |
proxy.config.ssl.CA.cert.path |
Specify the location of the certificate authority file that client certificates will be verified against. The default value is NULL. |
records.config file. bin directory. traffic_line -L to restart Traffic Server on the local node or traffic_line -M to restart Traffic Server on all the nodes in a cluster. The figure below illustrates communication between Traffic Server and an origin server when the SSL termination option is enabled for Traffic Server/origin server connections.
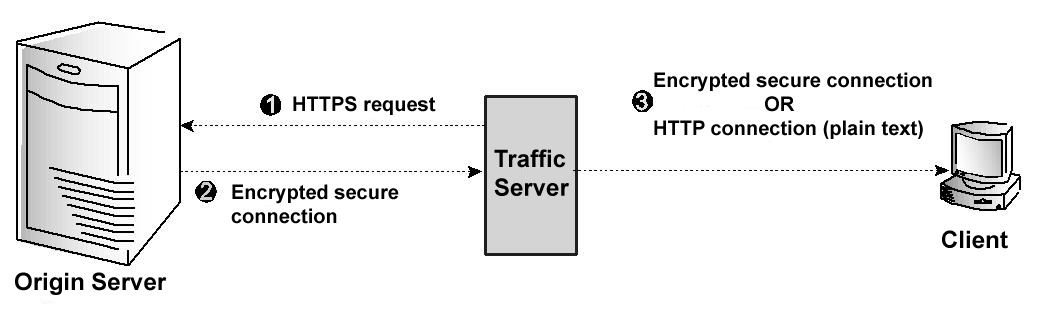
Traffic Server and origin server communication using SSL termination
The figure above depicts the following:
Step 1: If a client request is a cache miss or is stale, then Traffic Server sends an HTTPS request for the content to the origin server. The origin server receives the request and performs the SSL handshake to authenticate Traffic Server and determine the encryption method to be used.
Step 2: If Traffic Server is allowed access, then the origin server encrypts the content and sends it to Traffic Server, where it is decrypted (using the method determined during the handshake). A plain text version of the content is saved in the cache.
Step 3: If SSL termination is enabled for client /Traffic Server connections, then Traffic Server re-encrypts the content and sends it to the client via HTTPS, where it is decrypted and displayed. If SSL termination is not enabled for client/Traffic Server connections, then Traffic Server sends the plain text version of the content to the client via HTTP.
To configure Traffic Server to use the SSL termination option for Traffic Server and origin server connections, you must do the following:
records.config file located in the Traffic Server config directory. SSL Termination section of the file: | Variable | Description |
|---|---|
proxy.config.ssl.auth.enabled |
Set this variable to 1 to enable the SSL termination option. |
proxy.config.ssl.server_port |
Set this variable to specify the port used for SSL communication. The default port is 443. |
proxy.config.ssl.client.verify.server |
Set this option to 1 to require Traffic Server to verify the origin server certificate with the Certificate Authority. |
proxy.config.ssl.client.cert.filename |
If you have installed an SSL client certificate on Traffic Server, then set this variable to specify the client certificate filename. |
proxy.config.ssl.client.cert.path |
If you have installed an SSL client certificate on Traffic Server, then set this variable to the location of the client certificate. The default location is the Traffic Server config directory. |
proxy.config.ssl.client.private_key.filename |
Set this variable to specify the filename of the Traffic Server private key. Change this variable only if the private key is not located in the Traffic Server SSL client certificate file. |
proxy.config.ssl.client.private_key.path |
Set this variable to specify the location of the Traffic Server private key. Change this variable only if the private key is not located in the SSL client certificate file. |
proxy.config.ssl.client.CA.cert.filename |
Specify the filename of the Certificate Authority against which the origin server will be verified. The default value is NULL. |
proxy.config.ssl.client.CA.cert.path |
Specify the location of the Certificate Authority file against which the origin server will be verified. The default value is NULL. |
records.config file. bin directory. traffic_line -L to restart Traffic Server on the local node or traffic_line -M to restart Traffic Server on all the nodes in a cluster. You can install an SSL accelerator card on your Traffic Server machine to accelerate the number of requests Traffic Server can process. Traffic Server supports the Cavium accelerator card. If you opt not to use an SSL accelerator card, then you'll use your normal SSL library; if you install the Cavium card, then you'll use the library supported & provided by the card manufacturer.
records.config file located in the Traffic Server config directory. SSL Termination section of the file: | Variable | Description |
|---|---|
proxy.confg.ssl.accelerator_required |
Set this specify if an accelerator card is required for operation.
You may specify: You can verify operation by running |
|
Specifies if the Cavium SSL accelerator card is installed on (and required by) your Traffic Server machine:
|
records.config file. bin directory. traffic_line -L to restart Traffic Server on the local node or traffic_line -M to restart Traffic Server on all the nodes in a cluster.